
However, under the surface, they can provide total anonymity. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser.
Anonymity Requires Discipline
While disabling JavaScript might break the functionality of some websites, the enhanced security it provides is generally considered essential for navigating the potentially hostile environment of the dark web. Disabling JavaScript, especially on non-HTTPS sites (in “Safer” mode) or entirely (in “Safest” mode), is a widely recommended security practice when browsing the dark web. This is a non-standard HTTP header that website administrators can implement on their regular (surface web) websites to advertise if they also have an onion service counterpart.
Whatever your reasons for entering the dark web are, you must follow some crucial steps to ensure your safety so that you can access it in an entirely safe and anonymous way. They exchange sensitive information and data, and, at times, have to risk their lives or those of their informant if they don’t share data under the safety of the deep web. The dark web is designed to protect private information, keeping sensitive data out of the public eye.
Conclusion: Should You Use Dark Web Browsers?
The concept of an encrypted, hidden layer of the internet began taking shape in the 1990s. The dark web is notorious for hosting a wide range of cyber threats that pose significant risks to individuals and organizations. Other search engines like Haystak boast millions of indexed pages and advanced filtering options. Because of these privacy features, the dark web remains a hidden but active part of the internet ecosystem. Despite its negative reputation, not all activity on the dark web is malicious; some users rely on it as a tool for freedom of expression or to circumvent restrictions.
In rare cases, attackers can exploit an unsecure node to monitor Tor users or gain unauthorized access to accounts. As mentioned earlier, many websites consider Tor suspicious and block users entirely. Most websites have HTTP and HTTPS versions, but connecting to the former introduces a security vulnerability. You can also use DuckDuckGo to find onion sites across the Tor network. If so, it’s better to use the onion address instead of the standard one.
For journalists, students, researchers, and security professionals, it’s a powerful tool when used ethically and safely. Accessing the Dark Web using the Tor Browser is not just about exploring hidden parts of the internet—it’s about understanding privacy and cybersecurity in the modern world. You can’t search for .onion sites using Google. Tor (The Onion Router) Browser is a privacy-focused web browser that routes your traffic through multiple encrypted relays across the world, ensuring anonymity. These websites use special encryption protocols and are accessible only through anonymizing tools like the Tor Browser. The Dark Web refers to hidden websites that aren’t indexed by regular search engines like Google or Bing.
We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. The dark web is a very popular platform for journalists, political bloggers and political news publishers, and in particular, those living in countries where censorship shields most of the internet. The U.S. Army developed “onion routing” to protect intelligence communications online. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The core principle of the Tor network was first developed by U.S.

Step 2: Install Hyphanet
By the way, most have shipping services. The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not. Hidden Wiki’s not the only search engine online. If you’re feeling chatty, you can always access a chat room. Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff.
Separate Your Real Life From Your Online Persona
First, let me explain that this article is intended for users who want to use the dark web for legal and needed purposes, such as finding censored news, blocked websites, and other much-needed services. Content includes non-indexed websites, apps, and resources, which can include protected information such as, online banking, specialized databases, non-linked and password-protected websites, and more. The dark web is web content that exists on darknets, which are overlay networks on the internet that require specialized software, configurations, and authorization to access. Such data includes medical records, financial information, research papers, private forums and networks, and other content. The Tor Browser is the most commonly used tool to access .onion websites.
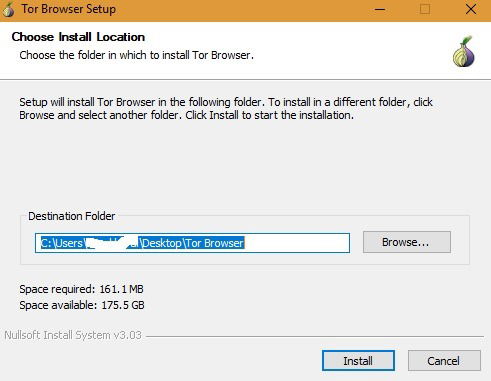
Start With The Basics: Preparing And Installing Tor
Whether you’re here out of curiosity or necessity, these steps will help you browse without getting burned. You’ll learn how to set up Tor Browser the right way, spot legit .onion links, and follow key safety checks to stay private. This guide breaks down exactly how to access the dark web without putting yourself at risk. The rankings and reviews we publish may also take into consideration the common ownership mentioned above, and affiliate commissions we earn for purchases through links on our website. The network is comprised of thousands of volunteer-run servers known as Tor relays. Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information.
Wrap-Up: Staying Safe While Accessing The Dark Web
- "People can accidentally give that away just by posting their real name, email address, or other identifying details, in a blog comment," notes Muffett.
- Underneath it are deeper layers that aren’t visible through normal browsing.
- “Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet.
- That is why the explorers post their content on the dark web forums rather than the surface web.
- Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC.
When the Tor Browser is launched, you will be brought to a purple homepage with a search field for the DuckDuckGo search engine in the center of the screen. This guide will teach you how to install the Tor Browser in Windows easily so you can access the Dark Web or browse the web anonymously. Your email address will not be published. Specifically, she’s crazy about the three C’s; computing, cybersecurity, and communication. Abeerah is a passionate technology blogger and cybersecurity enthusiast.
The Ultimate 2025 Guide To The Tor Browser
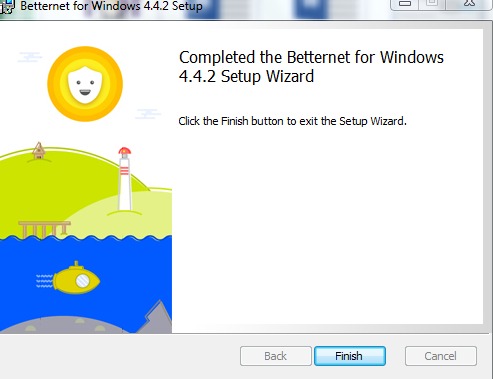
A VPN doesn’t encrypt traffic after it exits the Tor network. Your ISP still knows you’re using Tor, and entry nodes can see your real IP address. Your internet activity is still subject to exit node risks, so always use HTTPS and avoid entering any personal information on unencrypted sites. That means your ISP only sees encrypted VPN traffic and can’t tell you’re using Tor. Most dark web leaks happen when users skip basic safety steps or reveal too much without realizing it.
The users of the dark web are typically aiming to block governments from snooping on them. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”. The dark web addresses are a randomly-scrambled sequence that generates URLs, mostly hard to remember ones. While I know that none of my readers are looking to engage in any of the activities I’ve mentioned, I felt that it was important for my readers to be aware of the dangers that lurk on the dark web. To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section.
Top Free & Safe Dark Web Browsers In 2025: The Complete Guide
While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. So, once you’ve activated your VPN and your privacy is secured, it’s time to visit Tor’s official download page. Make sure that when you download the Tor file, it’s from their official website.
These sites are often closely monitored by law enforcement agencies and are illegal to access or participate in. After installation, you can use Tor to access the public internet as well as .onion websites. After your data is secured inside multiple layers of encryption, your web traffic is transmitted through a series of network nodes, called onion routers. Tor (The Onion Router) is a web browser that lets users access a network that anonymizes web traffic to provide private web browsing. One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity.



