As long as you avoid engaging with illegal content, you have nothing to worry about. In some countries, even viewing certain types of content can be a legal risk, so you should be careful about the sites that you visit. For example, journalists, whistleblowers, and privacy-conscious individuals often use it to communicate securely or access uncensored information in restrictive regions. Never sign in to any account linked to your real identity (email, social media, banking, etc.) while browsing the dark web. If you’re unsure about a link, do some research or ask trusted sources within dark web communities. Be cautious of random or obscure links — these could lead to dangerous or malicious websites.
How Organizations Can Protect Themselves From Tor-Based Threats
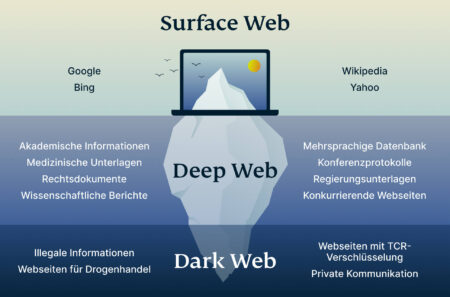
You’ll find the more dangerous content and activity at the dark end of the deep web. For this reason, users should be cautious when using their browsers. There are plenty of harmless reasons sites stay out of sight, and they won’t put you or your computer at risk. The open web makes up less than 4-5% of the internet, which is just the tip of the iceberg of the entire internet.
Internet Searches That Could Get You Arrested
Freebie VPNs will track their users' online usage, as they make money by selling this tracking info to advertisers and other nosy parties. Just remember, this only hides your browser-based activities and doesn’t hide any of your other online activities. Using a VPN is perhaps the easiest and most efficient way to protect your online travels from prying eyes, as it hides your real IP address, and encrypts all of your online traffic. There are several ways to protect your online activities from being tracked. All data is routed from the exit node through a secure VPN connection. This does not protect you from malicious exit nodes, as your internet traffic is unencrypted by the time it reaches its destination.
The dark web also offers access to blocked resources in countries with strict government censorship on the internet. Some users, such as whistleblowers or journalists working on sensitive issues in oppressive authoritarian governments, need privacy to carry out their activities. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Like Freenet, I2P has its own dark web that consists of websites ending in b32.i2p. It works as a decentralized, peer-to-peer network that emphasizes censorship resistance and complete anonymity.
Is There A Tor Browser For Android?
Always conduct your own research or check with certified experts before investing, and be prepared for potential losses. The content produced on this website is for educational purposes only and does not constitute investment advice or recommendation. The internet is huge—even in its shadows—it is possible to wander legally there. Used ethically, such as for privacy or study, one can search this area lawfully and safely. By encrypting communication before it gets to the Tor network, pairing Tor with a VPN gives a second degree of protection. Research of the dark web is legal as long as national or international laws are not broken.
How And Why Deepfake Videos Work — And What Is At Risk

Edward Snowden used the Tor global network on a regular basis. Arguably, the best-known tool used to access the dark web is the Tor Browser. While there are numerous VPN services that work well with Tor, I’ve found that NordVPN offers the best protection and compatibility, and keeps your personal information safe. A VPN’s ability to hide your Tor usage from your ISP and from government authorities makes for a valuable addition to your online privacy arsenal.

Conclusion: Access The Dark Web Safely And Responsibly
The dark web forms a small part of the larger deep web, which includes all parts of the internet not indexed by search engines. The dark web is rife with hidden links and malicious content, and a simple misclick can lead to legal trouble if you are not careful. Simply accessing the dark web is not illegal, but what you do there can lead to criminal consequences. Not to mention, law enforcement authorities can always request a person’s search data. It is perfectly legal to search anything online in most cases, but if those searches are linked to a crime or potential crime, you could get arrested.
This technology was instrumental in dismantling the Welcome to Video platform, a dark web site distributing child pornography, where investigators traced payments to arrest over 300 suspects worldwide. Blockchain analysis has become increasingly important in tracking cryptocurrency transactions linked to criminal activities. This topic is significant as it touches on privacy rights, cybersecurity concerns, and legal boundaries in an increasingly digital world. Explore the legal nuances of accessing the dark web, including potential penalties and jurisdictional differences. Whether you’re a privacy advocate, journalist, or curious user, using this guide as your foundation will allow you to navigate the dark web responsibly. Keeping your VPN and Tor Browser updated ensures you benefit from the latest security patches.
Report It To The Authorities (if It’s Safe To Do So)

We’ve found that Tor is an excellent way to keep your internet browser-based online activities undercover, although we’ve also seen how using the Tor Browser can bring unwanted attention. In addition, NordVPN offers Onion over VPN (think Tor over VPN), which routes your internet traffic through one of its servers, passes it through the Onion network, and then sends it to the internet. Then the Tor anonymity network relays further obfuscate your true location, as the browser relays your browser traffic through several relay locations. A VPN keeps all of your online activities – including your web browsing, online gaming, streaming, and file-sharing – undercover and safe from being tracked or recorded. The Tor Browser prevents your ISP from seeing what websites you’re visiting, but it does not prevent the ISP from seeing that you’re using Tor. If you need to protect or enhance your streaming, gaming, or torrenting activities, a Virtual Private Network (VPN) is a much better option as a secure connection to the net.
The attacks have led to the formation of other cybercriminal groups and Cyber Extortion. Dark web marketplaces often rely on Bitcoin, a cryptocurrency known for its anonymity and flexibility. Moreover, hackers who offer their services over the dark web have also targeted financial institutions and banks. The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group.
While Tor does a solid job anonymizing your traffic, there are still gaps, and that’s exactly where a VPN steps in. Not just to stay anonymous online, but to stop your ISP, government, or even opportunistic creepers from tracking your every move. Remember that no one can prevent all identity theft or cybercrime, and that LifeLock does not monitor all transactions at all businesses. Research what they offer and assess your privacy needs to make a decision about which dark web browser works best for you.
The Hidden Wiki
Implementing 2FA significantly reduces the risk of unauthorized access to your accounts, as it makes it much harder for attackers to bypass your security measures. Two-factor authentication (2FA) is a crucial security measure when navigating the Dark Web. By following these guidelines, you can significantly enhance the security of your online accounts. Creating strong and unique passwords is crucial for protecting your online accounts from unauthorized access. When encountering illegal activities on the Dark Web, it is crucial to take appropriate action. It is crucial to remember that engaging in illegal activities on the Dark Web can lead to serious legal repercussions.
Stick to tried-and-tested sites and do your best to avoid scams. Above all, it’s vital to go on the dark web carefully and sensibly. This internet space can be dangerous, but you can safely get on it by using a VPN and then connecting to Tor. Let’s summarize the most important points from this guide on how to access the dark web. Some sites are safe to use, especially those where you don’t need to provide sensitive information.
Why Use Tor?
- The Whonix Gateway VM handles Tor processes, and the Whonix Workstation VM runs user applications on an isolated network.
- However, third parties such as the government and your internet service provider (ISP) can see that you are using Tor.
- Don’t get Tor confused with a VPN though, which uses tunnels to protect your data from lurkers.
- Best of all, it’s jargon-free, personalized, and easy to use.
- Whatever your reasons for entering the dark web are, you must follow some crucial steps to ensure your safety so that you can access it in an entirely safe and anonymous way.
These services utilize unique web addresses ending with the .onion top-level domain, signifying that they are accessible only through the Tor network. While this may cause some websites to lose certain functionalities, the enhanced security is often considered a worthwhile trade-off, especially when navigating potentially risky parts of the internet. Websites within the dark web often utilize unique addresses ending in .onion, which are exclusive to the Tor network and cannot be accessed via standard web browsers.
Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you. Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down. As I mentioned previously, using the Tor Browser will slow down your browsing. While the Tor Browser does an excellent job of protecting your privacy and anonymity, you really shouldn’t use it as your daily driver browser.
But your tools are only half the story. We recommend that you use only the Tor browser to access the deep, dark web, if you must. When it comes to accessing the dark web (and safely), selecting a good dark web browser is critical.



