
Well, as long as you don't visit sites with underaged models or that engage in human tracking or that sell drugs and other illegal items. Tor was designed to protect American intelligence communications online. For totally hiding all of your online antics, you’ll want to also use a VPN. Just remember, this only hides your browser-based activities and doesn’t hide any of your other online activities. If top-notch privacy is your goal, yes, you can use the Tor Browser for all of your browsing.
Likewise, some websites allow Tor, but with frequent Captchas that can be annoying. Tor is slower than standard browsers because it routes your traffic through multiple servers. You can also use it if you don’t want your network administrator or ISP to be aware of your Tor usage. You can use a VPN if you’re in a country that restricts or heavily monitors Tor usage. Whenever you enter any domain into the address bar, your browser uses HTTP to find and request the data from the relevant server. A little typo can lead you to a clone designed to trick users into handing over sensitive data.
- Its clean and uncomplicated interface is straightforward to navigate, allowing you to easily toggle between anonymous and non-anonymous browsing.
- But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network.
- Anyone can access the dark web, and it’s not that complicated to do so.
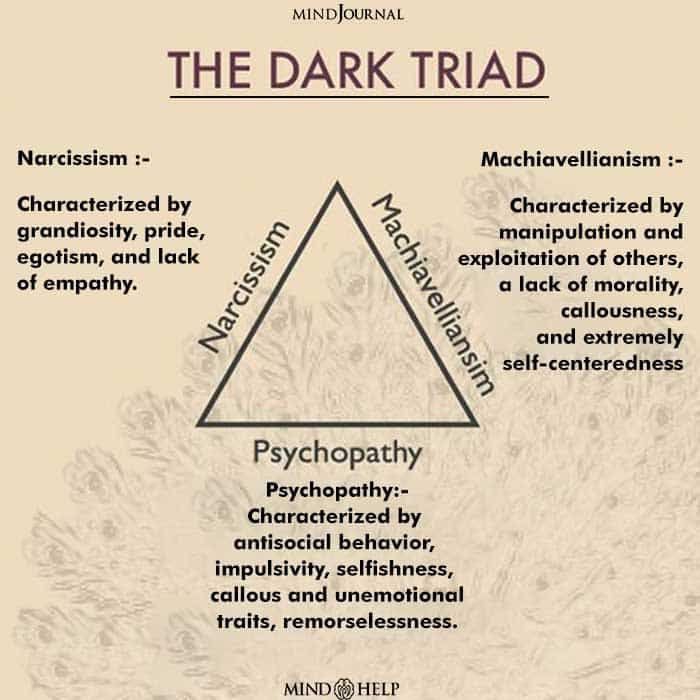
- The dark web refers to websites that are not on the regular internet but are instead hidden in a private network that is only accessible using specialized web browsers, such as the Tor Browser.
Tor Browser 1502 (14050esr) Screenshots (

Regardless of your browser, accessing the dark web carries inherent risks, including potential exposure to malicious software and illegal activities. We’ve listed the 10 best dark web browsers for 2025. This is not about fear; it’s about smart privacy. Discover the top 10 dark web browsers. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. You'll often see a sign in stores that says "look, don't touch," and it's not a bad adage to bear in mind as you navigate around the dark web.
Firewalls protect the content present in the Deep Web. The deep web is hidden from plain view, but most internet dwells in this layer. The second layer of the internet, also known as the Deep Web, exists just below the Surface Web.
How Do Dark Web Browsers Work?

I recommend exercising extreme caution and carefully researching any dark web sites you intend to explore. Darknet combines secure browsing, privacy protection, and detailed guidance, offering a powerful solution for navigating the dark web safely. Its layout engine displays online pages effectively on Android devices such as smartphones or tablets, delivering an optimized browsing experience. Upon visiting a website, Darknet retrieves the data seamlessly while maintaining user anonymity. Whether you are exploring academic content, legal data, or unique marketplaces within the dark web, the app’s structure ensures user safety and discretion. Darknet allows you to access the dark web and its hidden resources securely.
What Is The Onion Network?
The latest version has an in-built VPN feature that provides extra security. Opera can be used as a browser to access the deep web too with deep web login. It is a completely anonymous networking platform that you can use without an Internet connection too. Users can know which users can be trusted and which users are harmful, thereby protecting legitimate users from attacks and hacks.
#1 Install A VPN
It permits its users to know which users are trusted and which are not. Summing up, if you need to experience a mind-blowing dark web browsing with powerful features, you must definitely choose Whonix. As this browser is lightning fast apart from the fact that it uses the Tor network, it does not matter whether some malicious code or software bears root privileges. You will also be hit by remarkable differences in the levels of security while using this browser.
Requirements (Latest Version)
You can use this as a dark web browser iphone or dark web browser android. You must also check if you are connected to the Tor Network by visiting the check.torproject.org alongside using a premium VPN for additional privacy. Thus, you will have to configure the proxy access manually, which is very simple. Firefox requires to be routed for connecting through the Tor network to provide you with entirely anonymous web surfing.
Enhancing Your Security
It's a place where you'll find data leaks and illegal trades, but also legitimate, legal online activities users want to carry out without attracting the attention of law enforcement agencies or governments. Several accessible plug-ins can give a terrific experience to the users. The sites are identified by the Public Key than by IP address. The data is encrypted using a distributed network making the user totally untraceable to performing deep web login and surfing. I2P is a message-based network that sends the user’s traffic through distributed nodes making the user untraceable. It offers you the best level of anonymity and security.
Related Articles From The Safe Browsing Section
Whenever you type anything in a search engine on the clear web, say Google, it fetches the blogs, websites, videos, images, software, application and more. This is only possible as the Tor network provides both security and anonymity. The Tor network is an anonymous network that supports the existence of deep web and dark web websites.
The Tor Browser is a popular online anonymity tool among political activists and journalists who fear totalitarian governments monitoring or arresting them. The Tor Browser (“The Onion Router”) is a product of the Tor Project, which was founded on the belief that “internet users should have private access to an uncensored web.” If you are reading this, you’ve likely heard about how the Tor Browser can help protect your internet privacy and anonymity online. Most dark web browsers use The Onion Routing (Tor) network, where data is encrypted in layers and sent through multiple nodes.
A Free Program For Android, By ExploreDev
It also comes with several secure pre-installed software programs, including the Tor Browser. It acts like a shield for privacy, not a tool for anonymity. Epic is created with the Chromium source code, but all Google-specific tracking data code has been removed from it.

That said, there is one security setting you should get to grips with. Now you know why the development of the official Tor Browser for Android is great for privacy and security. However, the most recent versions can now route the traffic through Tor without Orbot. Orbot's node routing means it takes longer for your data to find its destination.
However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. If you want to buy something on the dark web, it’s a best practice to create a fake identity. Start the Tor browser by double-clicking on “Start Tor Browser” (for Windows) or “TorBrowser” (for Mac users). MacOS users will need to drag and drop the Tor Browser icon to the Applications folder. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder.



