Some of these sites can be found through regular web browsers, but you'll then need to switch over to Tor once you've got the onion links you want to follow. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you're looking for. The dark web comes with its own set of tools and services, including web browsers and search engines (which I'll get on to in a moment). It's a place where you'll find data leaks and illegal trades, but also legitimate, legal online activities users want to carry out without attracting the attention of law enforcement agencies or governments. To help you make educated choices about cybersecurity to keep you (and your data) safe and secure, by providing detailed, accurate, and practical information based on thorough testing. The links shared in this guide were working during testing, but legitimate services occasionally move to new URLs to enhance security.
You can also use its .onion link via the Tor network to access the site in restrictive countries, where it might be unavailable. The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites. Torch is one of the oldest dark web search engines, and it’s generally considered one of the safest. It has indexed more than 1.5 billion pages from over 260,000 .onion websites, so you’ll easily be able to find what you’re looking for.
Using Onion Over VPN — All You Need To Know
- Also, this unique browser offers users extreme flexibility.
- The Hidden Wiki is where most users start off when they first arrive on the Deep Web.
- For example, one can access DarkWeb via I2P, which is made possible through the Tor plugin of Orchid Outproxy.
- Accessing dark web sites isn’t hard, but doing it safely requires the right tools and awareness of common threats.
- Facebook’s .onion version might seem counterintuitive, but it serves a crucial purpose.
In recent years, several individuals have utilized the Tor browser to browse the surface of the net and explore the hidden recesses within the dark web. Some people use it for fair purposes, while others on the dark web carry out illegal activities. Moreover, the ability to remain anonymous has made the dark web a haven for people whose existence would be compromised by using the surface web.
Are All onion Sites Illegal?
For those who seek a platform where they can communicate without the fear of surveillance or data breaches, Riseup emerges as a top choice. The platform’s commitment to user privacy is evident in its robust encryption protocols and its stance against data logging. Riseup is not just another communication platform; it’s a movement. With its focus on user privacy and a clean, user-friendly interface, Ahmia has become an indispensable tool for many Tor users.
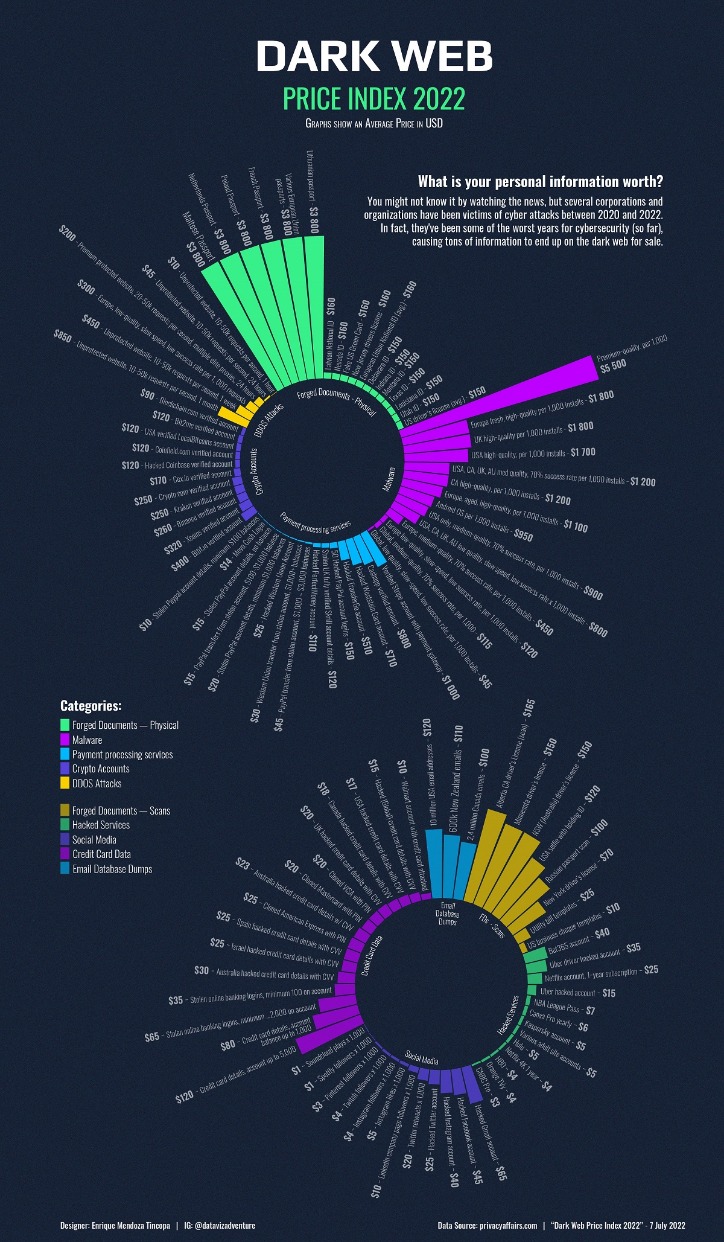
For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. Cybercrime services are more commonly sold through marketplaces, but you can usually find someone offering hacked servers, computer logins, and stolen data on such forums. Encrypted communication channels on the dark web allow users to message back and forth in an anonymous online environment. Of course, cybercriminals can also use them for nefarious purposes like discussing illegally shared interests, conspiring to commit crimes, or posting content deemed too unsavory for the clear web. If you do need to access a dark web website for legitimate reasons, you can check directories like The Hidden Wiki to help find options. Read on to learn more about the five main types of darknet websites and what they contain.
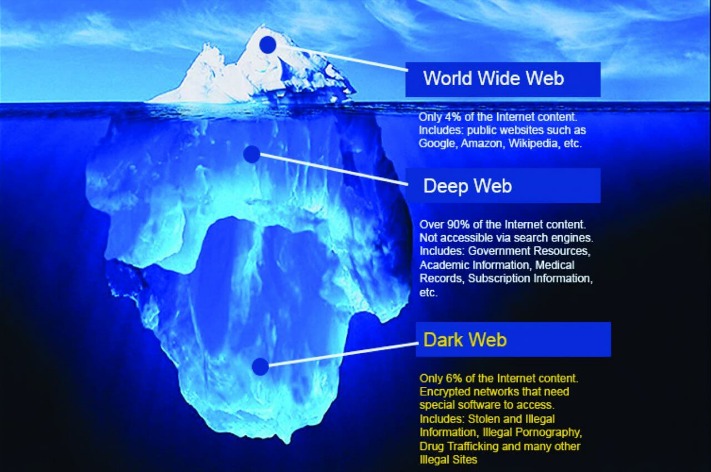
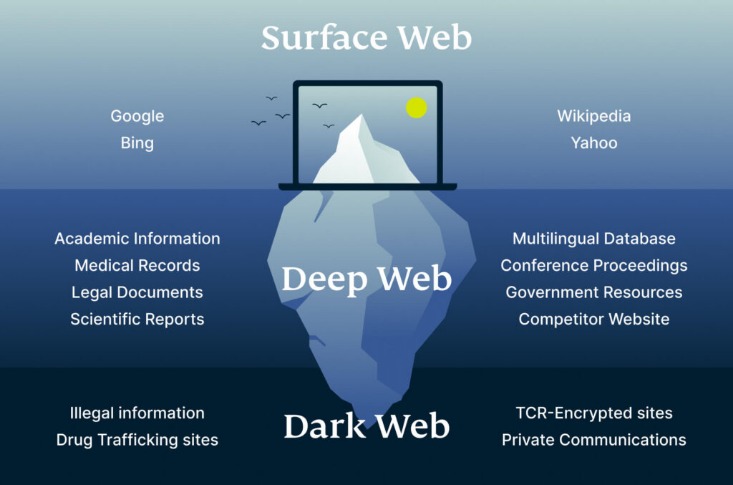
Tor Metrics
The users only have access to a fraction of the available data and web pages. Typically, any reference to the visible web will be to common websites with a familiar internet domain extension. But, how can you get access to all these websites, pages, and information on the deep web and dark web if they can’t be found through Google, Bing, or Yahoo? The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more. Content includes non-indexed websites, apps, and resources, which can include protected information such as, online banking, specialized databases, non-linked and password-protected websites, and more. The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines.
How Do OSINT Professionals Monitor Criminal Forums?
The task of anonymous data exchange is unmeasurable in the present digital scenario. The mere navigation of dark network links will not deliver your home to law enforcers. When it comes to providing privacy, mobile devices are notorious for their unreliable services. Shielding your network links with a degree of protection is always a better option.
The Beauty of Boys may be a creepy Tor link, not entirely morally correct either but it, without doubt, is one of the many Legal Tor links. It’s categorized into “Conspiracy theories”, “Suppressed Tech”, “Leaked Secrets” and so on; anyone can access and exchange information over there neither registration nor any personal details are asked for. It’s a site where users exchange information on the most controversial, or interesting topics in the least. As the name suggests, it lets people ask question and get hidden answers to them. Even though the categories are in some foreign language, the name of the books as well as the content is mostly English.
Of The Best Dark Websites Google Won’t Let You Find
Mozilla Firefox can access Tor if you configure it to use a Tor SOCKS proxy, but it’s not built for Tor’s threat model. This platform is ideal for peer-to-peer services, anonymous publishing, and apps that need persistent, distributed hosting. It uses different addressing and protocols than Tor, so .onion sites usually won’t work on I2P. Avoid clicking on random links shared on social media, chat apps, or marketing sites. Reputable platforms like SecureDrop and ProPublica publish official .onion domains for safe access. You need special software like the Freenet or Tor browser, which uses onion routing to encrypt data across multiple nodes.
Countries that heavily censor their internet traffic will necessitate a Tor Browser or VPN for people to access the surface web. The anonymity of the Tor network becomes necessary due to growing online privacy concerns today. Note that it is easy to find yourself in trouble when you act illegally and compromise other people’s security and liberty. For example, it protects your privacy and lets you view unverifiable content and services.
Best Dark Web Sites In 2024
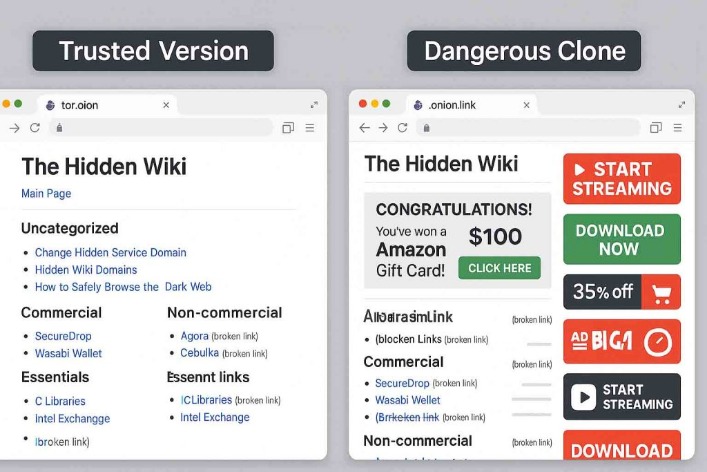
They help users find real dark web links, verify them through uptime tracking, and avoid dangerous clones. Back when reliable dark web search engines were limited, the Hidden Wiki served as a trusted compass for exploring the hidden layers of the internet. Hovering isn’t possible on Tor like in normal browsers, so it’s crucial to verify links through directories like dark.fail or onion.live before you trust them. Anonymity is one of the main reasons people explore dark web links, but it’s surprisingly easy to compromise your identity if you’re not careful. The dark web may offer access to valuable resources, but it’s also filled with traps, especially fake dark web sites designed to scam or harm unsuspecting users. These docs walk users through secure browsing, file storage, and messaging practices, all while maintaining the integrity of anonymous operating environments.
Cyble Strato Cloud Security
The site started as a fork of the ahmia search engine, this will remain a central part of the site. Although the site is still continually expanding and improving, it has become a significant resource on the Tor network. Not Evil is a reflection of what the community is looking for and what the community reports as abusive or inappropriate content.
- These alternatives aren’t necessarily safer or cleaner, they are merely alternatives for users wishing to keep their online activities as safe as possible.
- Your traffic is relayed and encrypted three times as it passes over the Tor network.
- A dark web search engine is a tool that helps users find content hosted on the dark web, specifically .onion websites, which are only accessible via the Tor network.
- This gives anonymity to .onion website owners and visitors.
- Their website is accessible on the clear web, but it also has a .onion site, allowing visitors to browse it anonymously, especially those living under oppressive regimes.
These connections can easily be reached by users who have basic knowledge of dark websites and computers. Installation of a specific browser package is required to browse dark web links. Yes, the TOR Project was a framework to shield the US Naval Research Laboratory’s private data from eavesdropping. There has to be a monitoring mechanism to track down illicit websites. They host illegal content and act as secure solutions for trading banned items. Post installation, surfing dark web links will be an easy affair.
Always double-check the spelling of a link and compare it against a trusted directory or the official announcement thread (if available on Dread or Reddit). One common tactic among scammers is URL spoofing — creating .onion addresses that look almost identical to trusted ones. These signatures are a powerful trust signal — they confirm the identity of the site’s operator and help you distinguish between real and fake versions. They list verified mirrors and often display digital PGP signatures posted by site administrators. Fortunately, there are trusted ways to verify whether a .onion link is legitimate.
How To Find Dark Web Websites
Adam is a senior security analyst who specializes in deep-dive research and practical security guides. The dark web often feels like the Wild West of the internet, a realm of anonymity, intrigue, and lurking danger behind every corner. Smartmixer made it harder to trace funds on the blockchain, although malicious actors could misuse such tools for illegal transfers.
As technology changes, so has the Tor network, which has moved from anonymity to a potent marker of digital independence. The deep web is always changing, influencing people’s access to knowledge, privacy protection, and secure communication. By using these verified links, you can dedicate your time to discovery and learning rather than wasting your time on broken or bogus onion links. Curated lists lead you to working tor links, reputable communities, and vetted (and hopefully safer) deep web resources. Visiting verified deep web links is a bit safer, but security really depends on your own behavior and choices.
Also, you must log in or have a specific IP address or URL to access the deep web content. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. For this reason, you cannot browse through these sites using your default search engine. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. This way, you can protect yourself from websites that want to steal your login details or cryptocurrency.



