
The dark web gets its name because it's private and secretive, but there are ways to know when your data's going out to the highest bidder. Sign in to your account to enter more information for monitoring. Our advanced monitoring technology goes beyond easily accessible sites and marketplaces, scanning private forums, the social web, the deep web, and the dark web to detect exposed information.
- If your data is found, the service provides detailed information about the breach, enabling you to take appropriate actions like changing passwords or terminating sessions.
- The types of personal information that are at risk on the dark web are credentials and personal identifiers that can be used for identity fraud or illegal access.
- Prioritize alerts based on dark web intelligence that indicates an imminent threat.
- Acronis Cyber Protect Cloud is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.
- Specialized tools and security analysts search for sensitive data such as leaked credentials, session tokens, financial records, and personal details.
Discover New Hacking Tools And Exploit Kits
LastPass, widely known for its password management services, integrates dark web monitoring into its premium plans. With additional features like antivirus and VPN, McAfee provides a layered approach to online security, covering up to 60 types of personal data and offering practical remediation solutions. The platform scans the dark web for compromised personal information and alerts users instantly to potential threats. Its dark web protection services provide continuous scans for sensitive information like passwords, financial details, and government IDs.
Who Needs Dark Web Monitoring Services?
Meanwhile, credit card protection with alerts ensures you stay informed about your financial data. With real-time alerts for credit card and ID breaches, Surfshark Alert offers timely warnings about potential financial risks. Take control of your digital security by investing in a reputable dark web monitoring service like McAfee Identity Protection Services to give you peace of mind and cyber resilience in an increasingly connected world. Dark web monitoring is the only service that alerts you to these third-party breaches before they become a crisis.
We balance automated blocks with rapid human-led investigations to manage threats. Proactive threat intelligence, original threat research and a world-class team of seasoned industry veterans. Get unlimited Incident Response with threat suppression guarantee – anytime, anywhere. Automate threat detection by integrating our API into your security stack.

What Sites Do Dark Web Scanners Monitor?
Now, let’s explore how all of this affects our dark web monitoring capabilities. Again, all of this is to say that we know what we’re talking about when it comes to cybersecurity. This core, overarching principle leads to a different perspective on cybersecurity. Since then, it has grown considerably and is still very much an expert-led organization, offering managed and professional services. Truesec has always been purely a cybersecurity company, built and led by experts founded in 2006 in Sweden. Therefore, we don’t attempt to differentiate based on data but rather on insights about how we can transform all this data into relevant and actionable intelligence for you as a customer.
Get alerted to compromised credentials, data leaks, and mentions of your brand, employees, and users. The offers on the site do not represent all available financial services, companies, or products. Banking services provided by CFSB, Member FDIC. Experian is a globally recognized financial leader, committed to being a Big Financial Friend—empowering millions to take control of their finances through expert guidance and innovative tools.
It’s Easy To Use
Censys is not just a dark web monitoring tool; it’s a comprehensive platform for assessing internet-facing asset risks. Investing in dark web monitoring solutions means adopting a proactive stance against cyber risks, protecting customers’ data, and adhering to compliance standards like GDPR or HIPAA. Waqas is a cybersecurity journalist and writer who has a knack for writing technology and online privacy-focused articles.
Truly Actionable Data

But you’ll want to go with the Premium or Family plan for customer support, one-to-many sharing, and other digital security features. It prompts you to change weak and reused passwords, and provides an overall security score based on the strength of those passwords. Originally developed as a password manager, LastPass has expanded its product to include Dark Web monitoring. Your Identity Guard “watchlist” can include over 70 pieces of personal information, including your SSN, driver’s license, healthcare ID, and more.
Unfortunately, because stolen data is often traded privately, scanners are unable to discover all of it. Aura keeps you safe from scams, fraud, and identity theft. Ryan Toohil has a BS in Computer Engineering from Virginia Tech and holds multiple patents in the web services domain. Aura’s Digital Parenthood Initiative is sparking a national conversation on healthy use of technology, giving parents the tools needed to support their kids. Please appreciate that there may be other options available to you than the products, providers or services covered by our service.
Switcher’s Guide To Mesh VPNs: Pros, Cons, And How To Set Up Key Features
It also actively monitors Active Directory, automatically prompting users to change their passwords soon after discovering a data breach. It is free software but accepts donations via bitcoins or PayPal to run its service. Besides this, you can also receive email notifications whenever your information is available in a recent data breach. It has a dedicated search bar where you can enter your email address or phone number to determine if it’s compromised in a data breach. The company continuously updates the database from thousands of darknet sites and other specific platforms like Tor, Discord, Paste sites, and Telegram.
Comprehensive Surveillance Of Key Dark Web Forums & Markets
Moreover, these tools play a vital role in protecting intellectual property and sensitive corporate data from the clutches of threat actors. By utilizing a dark web monitoring tool, organizations can effectively track and analyze dark web activity, extracting actionable intelligence that aids in threat hunting. By proactively engaging in dark web monitoring, businesses, and security teams can tap into a wealth of threat intelligence, giving them a strategic edge in threat hunting and cyber defense. Using dark web monitoring, it’s possible to automatically scan the dark web to detect and monitor potential threats and vulnerabilities that can compromise an organization’s digital security. SpyCloud is the trusted partner for security leaders, practitioners, and service providers across every industry when it comes to dark web monitoring solutions for consumer and enterprise protection.
Using threat intelligence to build a timeline to inform threat response actions AVFC takes its cyber protection to the Next Level with eSentire as its official cybersecurity partner. ESentire is The Authority in Managed Detection and Response Services, protecting the critical data and applications of 2000+ organizations in 80+ countries from known and unknown cyber threats. Open XDR with Agentic AI & machine learning that eliminates noise, enables real-time detection and response, and automatically blocks threats.
- OpenCTI is another open-source option for collecting, managing, and interacting with intelligence data.
- Use our free tool to see if your information has been leaked—and learn what to do about it.
- If you have an online account anywhere, your data is at risk of being part of a data breach.
- It is the perfect time to start if you’re not using any dark web monitoring services.
- Aura’s all-in-one digital security solution can keep an eye on all of this, so you don’t have to.
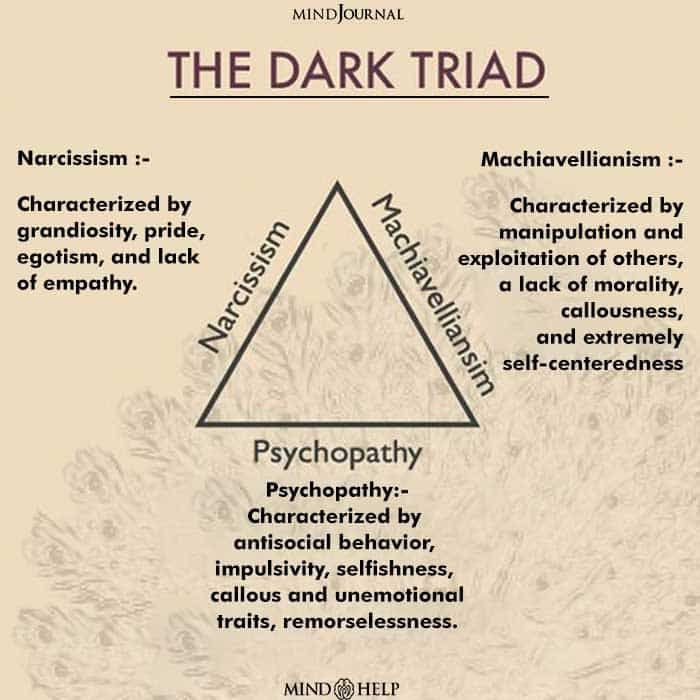
Compromised customer details, stolen financial data, and employee credentials usually get traded on these dark web forums. For companies, investment in these tools is sometimes the line differentiating between early detection and costly consequences. It ranges from selling stolen data and credit card information to even corporate secrets. While it doesn’t perform direct dark web operations like the other tools on this list, it plays a critical role in identifying traffic passing through Tor nodes, which can sometimes aid in investigations.
It's a proactive measure that helps reduce false positives -incorrect alerts of danger- and ensures higher quality alerts. Here, everything from credit card numbers to private health records can be traded. Newly identified vulnerabilities or exploits represent significant opportunities for threat actors, and these attack methods are discussed, developed, and sold in dark web forums and underground marketplaces. To make the best use of dark web intelligence, you want to be alerted only when new and relevant information emerges and be able to quickly determine what requires further investigation or escalation. These sites often harbor malicious software and compromised credentials, posing significant risks to individuals and organizations alike. These are rich sources of intelligence, often relevant to a broad spectrum of potential targets.
Prioritize alerts based on dark web intelligence that indicates an imminent threat. Searchlight’s proprietary technology helps security teams detect criminal reconnaissance and insider threats, so you can stop attackers from compromising your network. Your dark web alerts are always contextualized, with a complete picture of actor, location, and even real-time and cached access to the dark web data directly. Using advanced AI and analytics, our dark web monitoring tool automatically scans your organization’s attributes, such as domains and IPs, against over 475 billion deep and dark web records.



